Take Control of the Cyber War Against Your Dealership
AutoSuccess
JANUARY 21, 2025
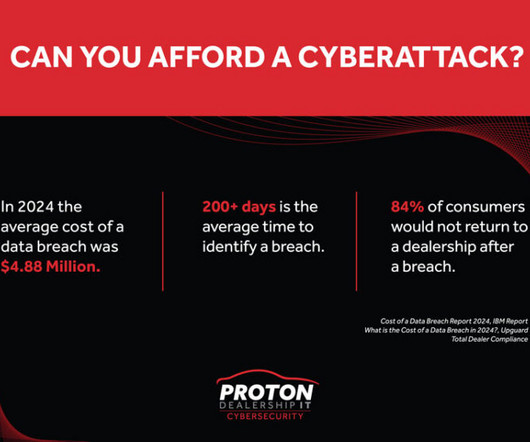
Every employee who handles data of any type must understand the security risks, be trained and be accountable for its proper and safe use. People-centric best practices are essential to refocus serious attention on employee responsibility and accountability in this cyberwar. So, what do you do? thieves, among other practices.

















Let's personalize your content